Get latest Nano firmware
- Download the latest firmware and save it to your Mac
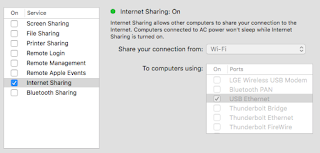
Configure USB Internet Sharing on your Mac
- Open System Preferences —> Sharing
- Enable USB sharing as shown in the image below
Configure Nano
Update Firmware
- Plug the Nano to the USB on your Mac. I just used the primary USB connector and not the additional Y cable USB connector, which seemed to work fine for the setup.
- Once the Pineapple boots up (the light stops flashing) connect to the WiFi access point that it creates using the Wifi Icon on your Mac menu bar or via System Preferences —> Network. The Wifi name looks like Pineapple_NNNN, where NNNN is from the MAC address printed on the bottom of the device.
- Connect to http://172.16.42.1:1471/ from a web browser
- Click "Continue" from that web page
- Hold the reset button for at least 3 seconds as directed (I configured the Nano with the WiFi on)
- From the web page click "Select File" and select the firmware you downloaded from the Pineapple site. Then click "Install."
- Wait a few minutes until the update finishes - the blue indicator light on the Nano should stop flashing. This will disconnect your Mac from the Pineapple WiFi.
Initial Device Configuration
- Reconnect your Mac to the Nano's Wifi Network (step 2, above)
- Follow to directions to continue "with WiFi enabled" by pressing reset button as directed.
- Set the password and SSID, for example MyPineappleWifi
- Click "Complete Setup" - which will disconnect you from the Nano's WiFi
Set Nano IP Address
Thanks to audibleblink for this post which describes configuring the Nano's network interface to work your Mac's internet sharing. Here are the steps:
- Reconnect to the Pineapple access point, i.e MyPineappleWifi
- SSH to your Nano from your Mac terminal:
ssh root@172.16.42.1- If you have installed other Pineapples and you get an SSH error, you may need to first clear the keys from your known_hosts file:
ssh-keygen -R 172.16.42.1
- From the shell of your Nano, configure the device's IP address and gateway. This will once again disconnect you from the Nano.
uci set network.lan.ipaddr='192.168.2.10'
uci set network.lan.gateway='192.168.2.1'
uci commit && rebootContinue Configuration
- Hard reboot: I had to unplug the Nano from USB, then reconnect to be able to connect to it after the network configuration. You shouldn't need to connect to the Nano's access point (i.e. MyPineappleWifi) at this point. You should make sure that your Mac is connected to a network and has Internet access though.
- Once your Nano reboots, try to reconnect via a web browser: http://192.168.2.10:1471/ (using the IP address you set in step 3, above)
- From the main Dashboard click "Load Bulletins..." button. If the data loads your Nano has an internet connection.
Next Steps
At this point if your Nano has an internet connection, you should be good to go. Feel free to let me know if there are any steps, issues or optimizations.